Why Model Governance Defines System Longevity
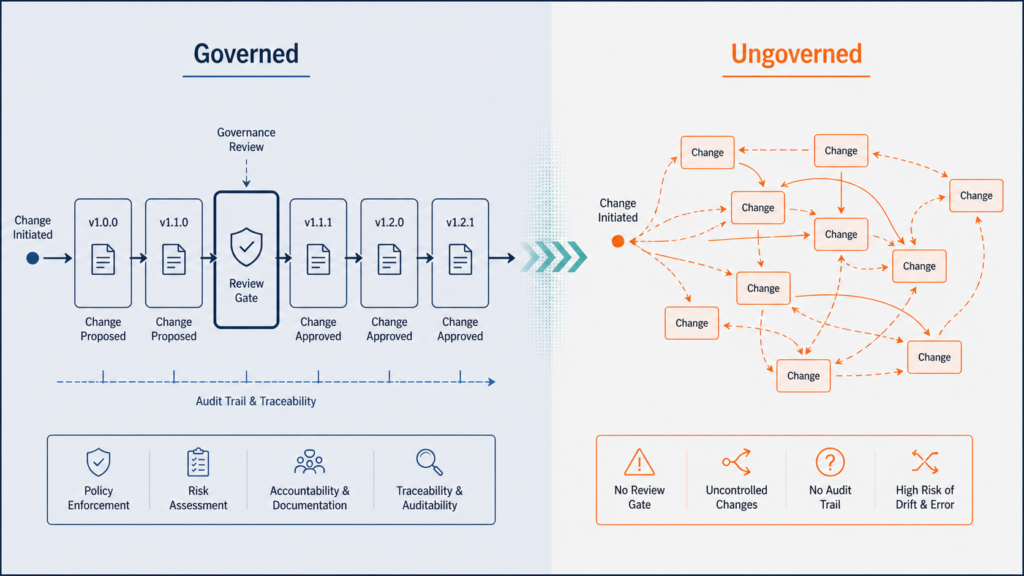
Model governance determines whether a systematic trading engine remains trustworthy over time. Most infrastructure discussions focus on signal quality, execution logic, or regime classification. However, the governance layer that controls how a model changes, who authorises those changes, and how prior versions stay accessible often receives the least design attention. This is a structural mistake. Without formal model governance, even well-designed systems degrade quietly as teams make undocumented adjustments, respond to recent performance, and gradually shift the engine away from its original specification.
Systematic trading infrastructure requires more than well-designed entry logic. It requires a disciplined framework for managing change itself. Furthermore, every modification to a trading model, however small, carries the potential to shift behaviour in ways that only become visible under stress. Model governance addresses this risk directly by establishing change control protocols, versioning standards, and review cadences that preserve system identity through its operational lifecycle.
The discipline of model governance sits at the intersection of engineering rigour and institutional accountability. Consequently, this article examines the core components of a change control and versioning framework, how review cycles enforce discipline, and why governance infrastructure is not optional for serious systematic trading operations.
What Model Governance Actually Governs
Model governance covers more than rules about when a model may change. Specifically, it defines the boundaries around three distinct activities: modifying parameters within an existing design, restructuring the model’s logic architecture, and deploying new model versions into live environments. Each activity carries a different risk profile and therefore requires a different authorisation standard. Treating all three as equivalent creates the conditions for structural drift without any single event appearing to warrant a formal review.
Parameters Versus Architecture in Governed Systems
Parameter changes appear minor on the surface. However, their cumulative effect across multiple sessions can shift the model’s behaviour profile significantly. For this reason, governed frameworks distinguish between within-tolerance parameter updates, which require documentation but not full review, and structural changes, which require formal sign-off before deployment.
Architecture changes represent a different category of risk. These modifications alter how the engine processes market data, filters conditions, or generates its output. As a result, even a change framed as an optimisation may introduce previously untested interactions between components. Consequently, the framework treats architecture changes as requiring pre-deployment testing, rollback plans, and documented rationale before they go live. This classification prevents the common mistake of treating a structural change as a routine parameter adjustment simply because the modification appears small in isolation.
Deployment Authority Under Model Governance
No governance system functions without clear authority structures. Specifically, model governance frameworks designate who holds deployment authority, under what conditions approval applies, and whether emergency changes may bypass standard review. Without these designations, the governance layer exists in documentation only and carries no operational weight.
In practice, well-designed frameworks separate the person who proposes a change from the person who approves it. This separation reduces the probability that recency bias or drawdown pressure drives undocumented modifications. Additionally, it creates a visible accountability chain that supports institutional review and satisfies the evidence requirements of external oversight.
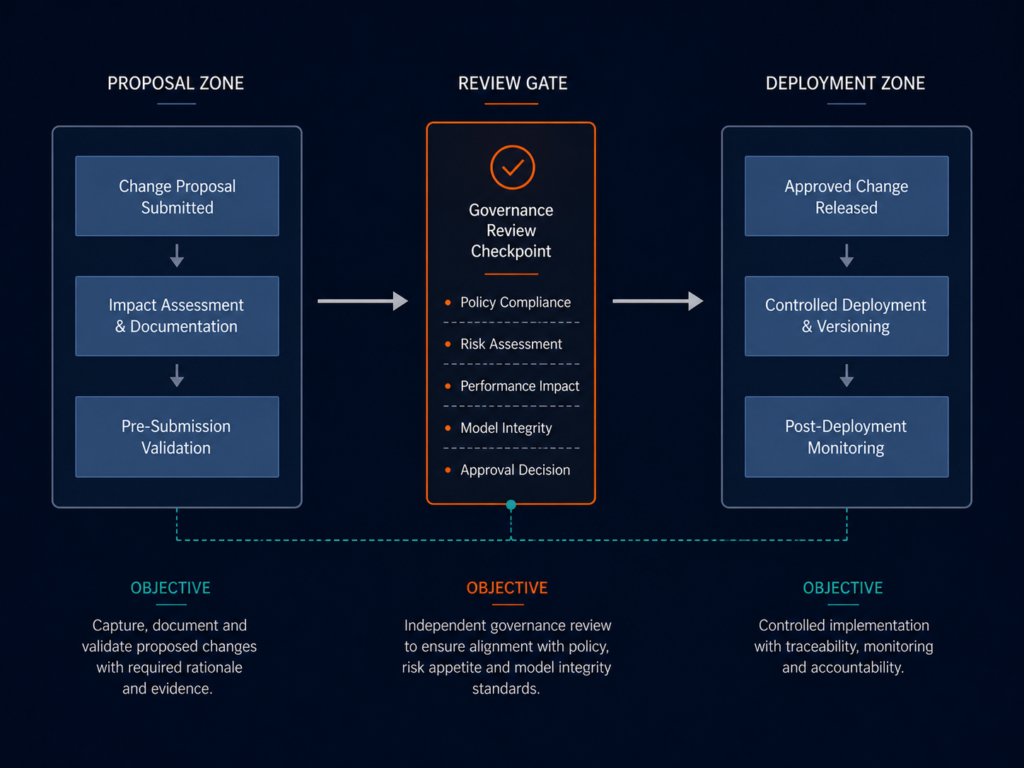
Change Control as a Model Governance Discipline
Change control in systematic trading is not bureaucratic friction. Rather, it is the mechanism that prevents a model from accumulating small undocumented changes that collectively alter its character without anyone noticing. Model governance formalises this protection by requiring written rationale, pre-deployment testing evidence, and post-deployment monitoring triggers for every change, regardless of how minor the modification appears at the time.
Why Undocumented Changes Accumulate
Trading systems face continuous pressure to respond to recent results. When a model underperforms in a given environment, teams often feel compelled to adjust. However, without change control, these adjustments stack invisibly. Over six months, a model may receive fifteen small parameter edits, three logic patches, and two filter revisions. None of these individually appear significant, but their combined effect reshapes the engine’s behaviour silently, disconnecting it from its original specification without any single change appearing to justify a formal review.
Change control prevents this accumulation by making each adjustment visible, attributed, and reversible. Furthermore, it forces proposers to articulate why a change serves the model’s long-term specification rather than simply responding to last month’s results. This discipline produces a secondary benefit: teams develop a clearer understanding of what the model is designed to do, because every proposed modification must be evaluated against that documented purpose.
Change Logs as Accountability Records
A well-maintained change log does more than record history. It provides the evidence base for evaluating whether a model’s current behaviour reflects its documented specification or has drifted from it. Additionally, change logs support institutional conversations with allocators and risk committees who need to verify that the model they reviewed is still the model operating in their capital’s interest.
Effective change logs in a governance framework contain the change date, the specific component modified, the rationale, the test results, and the name of the authorising party. Consequently, each entry functions as an accountability record rather than a simple administrative note. In practice, teams that build this discipline from the beginning find that change logs become one of the most useful internal resources for diagnosing behaviour shifts and communicating infrastructure decisions to institutional stakeholders.
Versioning Within Model Governance Frameworks
Versioning provides model governance with its most practical enforcement tool. Rather than allowing continuous undocumented change, versioning treats the model as a discrete artefact that advances through numbered iterations. Each version carries its own specification document, test suite, and deployment authorisation record. In this way, the model’s history becomes navigable, not merely traceable.
Version Numbering in Model Governance
Model governance frameworks typically apply a two-level versioning structure: major versions for structural changes and minor versions for parameter updates. This structure creates an unambiguous shared language for internal teams and external reviewers.
For example, a move from version 2.0 to version 3.0 signals a fundamental change to the model’s logic or architecture. By contrast, a move from version 2.1 to version 2.2 signals a validated parameter refinement within an existing architecture. Additionally, this structure makes rollback procedures unambiguous: if version 3.1 underperforms against its specification, the rollback target is version 3.0, and the precise differences between the two remain documented and accessible. Teams therefore face no ambiguity about what reverting to a prior state means in operational terms.
Rollback as a First-Class Governance Capability
Governance frameworks must treat rollback not as a failure response but as a designed capability. Specifically, every version deployed must have a tested rollback path. Teams should verify that reverting to a prior version restores previous behaviour within a defined tolerance window before the new version goes live.
The rollback decision itself requires documentation: what triggered it, who authorised it, and what post-rollback monitoring applied. Furthermore, without rollback capability, version control provides only historical record. With rollback as a first-class capability, the governance framework provides genuine operational insurance against deployment errors and unexpected behaviour changes. In this way, rollback transforms versioning from an archival practice into an active governance instrument.
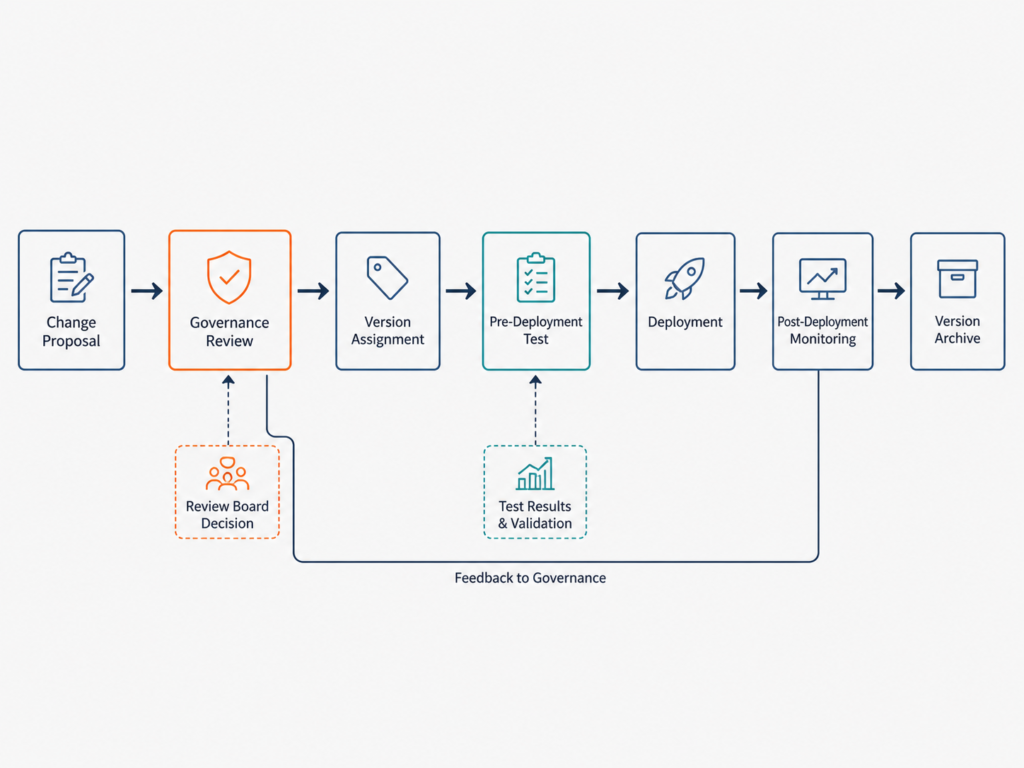
The Review Cycle: Cadence and Purpose
Governance does not function through one-off reviews. Instead, it requires scheduled review cycles that confirm the model’s behaviour remains aligned with its specification, its documentation remains current, and its operational context has not materially changed. The review cycle is therefore the recurring mechanism that keeps governance active rather than static.
Scheduled and Triggered Reviews
Systematic governance frameworks use two types of reviews. Scheduled reviews occur at fixed intervals, typically quarterly, and examine the entire model against its specification. Triggered reviews occur when specific conditions arise: a drawdown breach, a behaviour anomaly flagged by the monitoring pipeline, a change in execution environment, or a new market regime.
In practice, triggered reviews carry more operational weight than scheduled ones. Consequently, framework designers must define in advance what conditions trigger a review, who must participate, and what output the review must produce. This pre-definition prevents triggered reviews from being handled informally precisely when the pressure to act quickly is highest. Additionally, pre-defined trigger conditions remove ambiguity about whether a given event warrants a formal review, which is important during periods of elevated market stress when decision quality tends to degrade.
Documentation Standards for Review Outputs
Every scheduled and triggered review must produce a written output. Specifically, the review output documents whether the model passes or fails against its behavioural specification, what action follows if it fails, and when the next review will occur. Governance frameworks that produce verbal-only review conclusions cannot support institutional accountability standards, because verbal conclusions leave no verifiable record of what was assessed or what decisions were taken.
Documentation also creates the institutional memory that survives personnel changes. Additionally, it prevents the common failure mode where governance depends on a single individual’s informal knowledge of the model’s history. In a systematic trading operation, that individual eventually moves on. Therefore, the governance framework must function independently of any specific person’s memory or presence.
Human Authority in Model Governance
Systematic trading relies on pre-committed rules to enforce discipline before emotion or recency bias can intervene. Model governance extends this same principle to the change management layer. Rather than allowing the model’s operators to modify parameters in response to short-term pressure, governance frameworks require changes to pass through a review gate that operates independently of the trading decisions themselves.
Understanding pre-commitment rules in systematic trading provides important context here. The same structural discipline that governs entry decisions must also govern the process of modifying those decisions over time. In this sense, governance is simply pre-commitment applied to infrastructure rather than to trade execution.
Separating Decision Rights in Model Governance
Decision rights in model governance separate three roles: the proposer, the reviewer, and the deployer. In some frameworks, these roles belong to different individuals. In others, the same individual holds multiple roles but applies different procedural requirements to each.
The critical design principle, however, is that no single person should propose, approve, and deploy a model change without any independent check. This separation prevents the most common governance failure in systematic trading: a practitioner who manages the model making undocumented modifications during a drawdown period, rationalising each change as a necessary optimisation, and gradually converting a systematic engine into a discretionary one. Furthermore, separated decision rights create a natural friction that slows impulsive changes, which is precisely the friction a disciplined framework needs to remain effective under pressure.
Override Protocols and Their Limits
Governance frameworks must include clearly bounded override protocols. Specifically, these protocols define under what conditions a human override of the model is permitted, what the override must include by way of documentation, and how the override gets reviewed after the fact. The framework does not prevent all overrides. Rather, it ensures no override operates outside a documented structure.
This approach aligns with the core principle that system integrity in trading infrastructure depends on structural discipline rather than individual restraint. An engine that maintains its behaviour because governance protocols prevent undocumented change is more reliable than one that maintains behaviour because its operators happen to be disciplined on a given day. Moreover, this distinction matters to institutional stakeholders who want to assess governance quality independently of the personalities currently running the operation.
Model Governance Across Expanding Markets
Systematic trading engines operate across varied market conditions. Consequently, model governance frameworks must account for how behaviour changes are authorised during periods of high stress, low liquidity, or regime transition, when the pressure to make undocumented adjustments is highest. A governance framework that functions only during normal market conditions provides incomplete protection.
Regime-Aware Change Control
Governance frameworks that apply uniform change control across all regimes risk becoming either too restrictive during stable conditions or too permissive during stress. Instead, a regime-aware structure defines different authorisation thresholds for different environments. A parameter change that requires only documentation during normal conditions may require full committee review during a period of elevated volatility or unusual market structure.
This calibration does not weaken governance. Rather, it strengthens it by ensuring that the review standard matches the risk level of the operating context. Furthermore, regime-aware change control prevents the common failure where governance protocols written for normal conditions get bypassed during stress precisely when the risk of undocumented change is greatest. In practice, teams that define regime-sensitive thresholds in advance find that their governance framework remains functional under the exact conditions where informal approaches collapse.
Cross-Market Model Governance Requirements
As systematic engines expand across multiple venues, model governance frameworks must address how change control applies when the same underlying logic runs in different execution environments. A parameter change validated for ASX microstructure may not carry the same behaviour profile in the US equity market. Consequently, governance frameworks must specify whether change authorisation applies per-market or across all markets simultaneously.
In practice, well-designed frameworks treat the same logic running on different data interfaces as separate deployments, each requiring its own version record and behaviour verification before the change propagates. This discipline preserves the model’s identifiability across markets regardless of how its execution context differs. Additionally, it prevents a change validated in one environment from silently altering behaviour in another where the conditions differ in consequential ways.
Infrastructure Requirements for Durable Governance
Governance does not emerge from process alone. Rather, it requires dedicated infrastructure: specific tools and systems that make change control, versioning, and review cycles operationally feasible rather than aspirationally documented.
Infrastructure Components for Governance
A governance framework requires at minimum: a version control repository that treats model specifications as first-class documents, a change log system that captures all modifications at the component level, a pre-deployment test suite that validates each version against its specification before live deployment, and a post-deployment monitoring feed that flags behaviour divergence after a change goes live.
Teams that lack these infrastructure components often attempt to manage changes through spreadsheets, email threads, or meeting notes. Furthermore, these approaches consistently fail under the operational demands of a systematic trading environment. The governance infrastructure must be as reliable as the trading infrastructure it governs. As such, infrastructure investment in governance tooling is not optional overhead but a foundational requirement for operating a credible systematic engine.
Governance Readiness as an Institutional Standard
Institutional allocators increasingly treat model governance as a diligence criterion rather than an optional feature. They want to understand who controls model changes, what evidence supports each version deployment, and what the rollback path looks like when performance deviates from specification. Therefore, a systematic trading operation that cannot answer these questions with documented evidence faces a structural credibility gap regardless of its returns history.
Governance readiness means that every change to the trading engine, from a minor parameter adjustment to a full architecture revision, leaves a documented trace that supports independent verification. This standard is achievable with disciplined infrastructure design from the beginning of the system’s operational life. In this way, governance readiness becomes a foundation that accumulates value over time rather than a retroactive exercise applied once institutional scrutiny arrives.
Conclusion
Model governance is not a constraint on innovation. Rather, it is the framework that makes systematic change possible without compromising system identity. Change control prevents undocumented drift. Versioning creates a navigable history. Review cycles enforce accountability over time.
Together, these components ensure that a model operating in month eight resembles the model specified at deployment, not a sequence of informal adjustments layered over its original design. For systematic trading infrastructure to earn institutional trust, it must demonstrate that its governance layer matches the rigour of its execution layer. Governance provides that demonstration through structure, documentation, and verifiable discipline rather than performance alone.
Continue learning about systematic behaviour frameworks and how structural discipline underlies every layer of durable trading infrastructure.
About the Author
Dovest publishes institutional research on systematic trading infrastructure, behaviour-first frameworks, and governance architecture. All content reflects foundational principles and engineering methodology rather than investment advice or performance claims.
Disclaimer: This article provides educational content on systematic trading infrastructure and governance frameworks. It does not constitute financial advice, investment recommendations, or performance guarantees. Systematic trading involves risk. Past methodology does not guarantee future results.